Articles Tagged: Human and societal aspects of security and privacy
Articles & Features
SECTION: Features
From individual consent to collective refusal
Big tech companies have been found to misuse personal data, often collected without consent. What can the public do to change unjust collection and use of their personal data, and what role can computer scientists play in these efforts?
By Jonathan Zong, December 2020
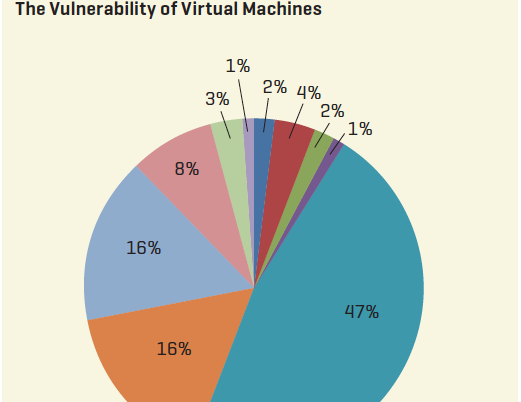
Cyber security in Africa: The boring technology story that matters
Cybersecurity involves protection of computer systems from theft, damage, or manipulation to the hardware, software, or the data contained on them. A limitless cyberspace, little to no boundaries, and eroding national borders is making Africa vulnerable to cyber threats and potential harms. Cybersecurity represents serious economic and national security challenges, which need to be properly defined and contextualized.
By Hood Mukiibi, November 2019
SECTION: Features
Autonomous infrastructure for a suckless internet
How can we promote an internet that respects human rights? Investing in autonomous infrastructure built and operated by politically motivated techies, who put their skills at the service of the public interest, may be the answer.
By Stefania Milan, July 2018
Routes to rights: internet architecture and values in times of ossification and commercialization
This article discusses the consequences of the commercialization and evolution of the Internet infrastructure, and how it affects our ability to exercise human rights online.
By Niels ten Oever, Davide Beraldo, July 2018
SECTION: Features
Journalism with flying robots
The use of unmanned aerial drones will revolutionize news reporting, but many issues need to be resolved before things can really take off.
By Matt Waite, March 2014
DEPARTMENT: Labz
Cryptography, security and privacy (CrySP) research group
By Atif Khan, December 2013
DEPARTMENT: Blogs
The New Firefox Cookie Policy
Stanford grad student Jonathan Mayer discusses cookies, Web tracking, and changes to Mozilla's cookie policy.
By Jonathan Mayer, September 2013
SECTION: Features
What is Public and Private Anyway? A Pragmatic Take on Privacy and Democracy
Revealing private content on the Web can also spark public engagement. To understand this, we need to challenge our common sense notions of privacy and democracy.
By Andreas Birkbak, September 2013
Something Bad Might Happen: Lawyers, anonymization and risk
The line between personal and anonymous information is often unclear. Increasingly it falls to lawyers to understand and manage the risks associated with the sharing of "anonymized" data sets.
By Marion Oswald, September 2013
Personal, Pseudonymous, and Anonymous Data: The problem of identification
Why defining what counts as personal data is important for data protection and information sharing.
By Iain Bourne, September 2013
Talking 'Bout Your Reputation
People think they want anonymity, but actually desire privacy. But how do we reframe the debate surrounding privacy and security? Perhaps technology is the answer.
By David Birch, September 2013
An Illustrated Primer in Differential Privacy
The vast amounts of data that are now available provide new opportunities to social science researchers, but also raise huge privacy concerns for data subjects. Differential privacy offers a way to balance the needs of both parties. But how?
By Christine Task, September 2013
Cynthia Dwork on Differential Privacy
Distinguished Scientist at Microsoft Research, Dr. Cynthia Dwork, provides a first-hand look at the basics of differential privacy.
By Michael Zuba, September 2013
Profile: Jessica Staddon
Managing Google's privacy research
In this profile, Jessica Staddon discusses managing privacy research for one the world's best-known technology corporations.
By Adrian Scoică, September 2013
DEPARTMENT: Labz
CyLab Usable Privacy and Security Laboratory (Pittsburgh, PA)
CUPS, a research lab at Carnegie Mellon University, is dedicated to addressing the broad array of challenges collectively called "usable privacy and security."
By Rich Shay, September 2013
Security, anonymity and trust in electronic auctions
By Jarrod Trevathan, May 2005
DNA smart card for financial transactions
In this paper, a secure environment for electronic commerce is introduced. The environment is formed via a synthesis of biometrics consumer authentication with a security token. Such a token is a smart card containing cryptographic keys and a cryptographic microprocessor for data encryption. The keys are used to further authenticate the possessor of the card as the actual owner and also to facilitate secure electronic financial transactions. New technologies like these bring benefits to society by enhancing the standard of living, however, numerous challenges are introduced [1].Biometrics is a Greek composite word stemming from the synthesis of bio and metric, meaning life measurement. In this context, the science of biometrics is concerned with the accurate measurement of unique biological characteristics of an individual in order to securely identify them to a computer or other electronic system. Biological characteristics measured usually include fingerprints, voice patterns, retinal and iris scans, face patterns, and even the chemical composition of an individual's DNA [9].
By Sofia Gleni, Panagiotis Petratos, September 2004
Multilevel security
By Stephany Filimon, April 2004
E-commerce recommenders
By Ana Gil, Francisco García, December 2003
Cookies
By Michael Nelte, Elton Saul, September 2000
Public key cryptography
By Pradosh Kumar Mohapatra, September 2000
Getting started with PGP
By Kevin Henry, July 2000
Protecting the integrity of agents
By Michael J. Grimley, Brian D. Monroe, June 1999
Electronic voting
By Lorrie Faith Cranor, April 1996